
Analyzing Apache Log Files
The server access log records all requests processed by the server. The location and content…
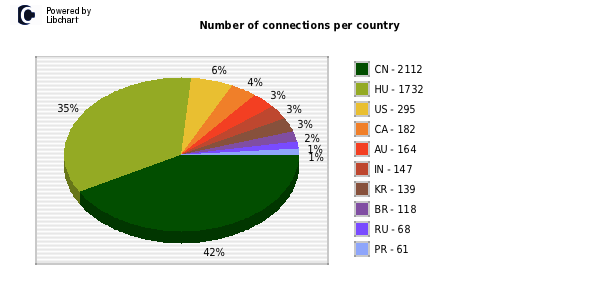
Honeypot Data Analysis
I’ve recently analysed a range of Honeypot data relating to about 3 months of malicious…


Free content from Internode
http://freezone.internode.on.net/ I’ll be using this page for the variaous media and streaming boxes we have. http://www.internode.on.net/residential/entertainment/unmetered_content/…

IP TV related links
Recently I have been tweaking our ADSL 2+ Internet connection (modifying line attenuation, etc.) and…

The Internet is the modern day electricity
Recently I have been been sorting through some of my old electronic engineering books and…
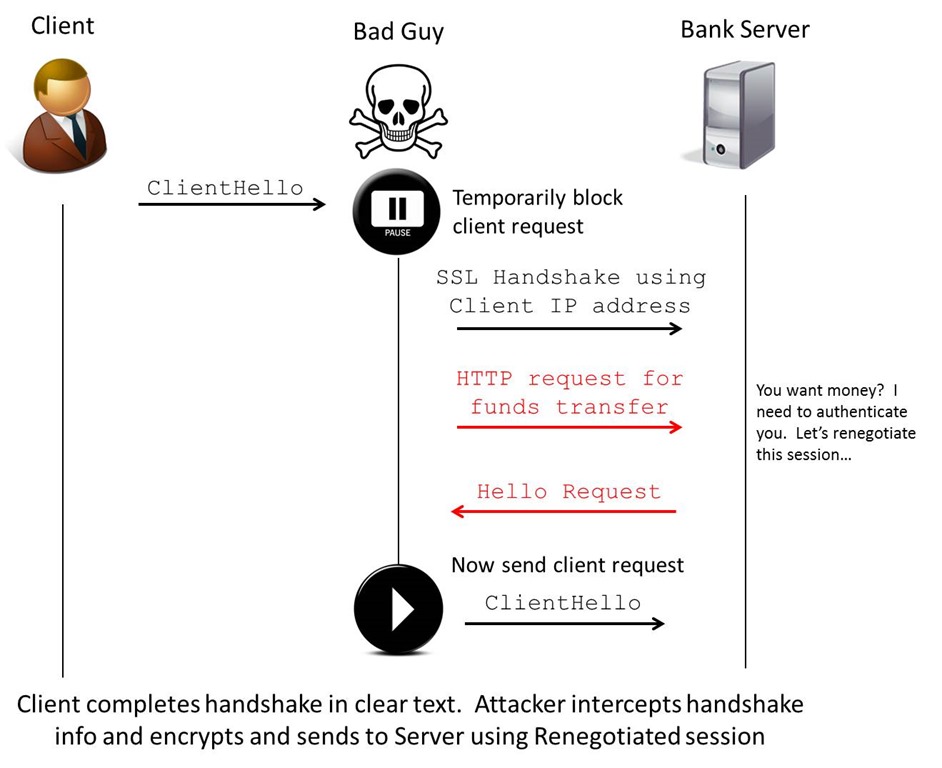
SSLv3 / TLS Man in the Middle vulnerability
Recently I have been looking into the vulnerabilities in the TLS negotiation process discovered late…
Nmap Examples
Some Nmap examples I thought I would post. Scanning past Watchguard Firewalls: nmap -sS -iL…

